How to Automate Video Access Control with SCIM, AD Sync, and RBAC
by Ali Rind, Last updated: May 6, 2026 , ref:
Managing video platform access manually stops working the moment your organization passes a few hundred employees. New hires wait days for access. Departing employees retain access for weeks. Permission drift accumulates until nobody is sure who can see what.
This guide covers how to automate video access control using SCIM provisioning, Active Directory synchronization, and group-based permission rules so that the right people have the right access without IT intervention on every change.
The Problem with Manual Video Access Management at Scale
In organizations with 500 or more employees, manual access management creates three persistent problems.
Onboarding delays. A new hire in the sales department needs access to product training videos, recorded webinars, and sales enablement content. If that access requires a manual IT ticket, provisioning, and group assignment, it can take days. The employee either waits idle or works around the system by asking colleagues to share links directly.
Orphaned accounts. When an employee leaves, their identity provider account gets disabled. But if the video platform is not connected to that identity provider, their video account stays active. They may retain access to proprietary training content, recorded executive communications, or confidential project updates.
Permission drift. An employee moves from Engineering to Product Management. Their old video access stays intact and new access gets added on top. Over time, accumulation means people have access to content well outside their current role. In regulated industries, this is an audit finding waiting to happen.
Manual processes do not scale. Every new hire, departure, and role change multiplies the maintenance burden on IT. This is a recurring challenge for any organization evaluating enterprise video library management software at scale.
What SCIM Does for Video Platforms
SCIM (System for Cross-domain Identity Management) is a protocol that lets your identity provider automatically push user lifecycle events to connected applications, including video platforms.
When SCIM is configured between your identity provider (Azure AD, Okta, Ping Identity, OneLogin) and your video platform, the following happens automatically:
- New user created in the identity provider. The video platform creates a corresponding user account, assigns the correct role, and places them in the right groups. No IT ticket needed.
- User deactivated or deleted. The video platform disables or removes the account. Access is revoked immediately, not whenever IT remembers to clean up.
- User attributes change. If a user's department, title, or group membership changes in the identity provider, those changes propagate to the video platform. Permissions update accordingly.
SCIM eliminates the gap between identity events and platform access. The identity provider is the single source of truth, and the video platform stays synchronized. For IT teams evaluating platforms, SCIM and SSO integration rank among the most critical enterprise requirements.
What AD/Entra ID Sync Enables
Active Directory (or Microsoft Entra ID) synchronization goes beyond basic user provisioning. It maps your existing organizational structure directly onto the video platform's content access model.
Here's what that looks like in practice:
- Organizational groups map to content categories. The "Marketing" group in Active Directory automatically gets access to the Marketing video category. When someone joins the Marketing group in AD, they see Marketing content in the video platform immediately.
- Security groups map to portals. If your organization runs separate branded video portals (one for internal training, one for customer-facing content, one for partner enablement), AD security groups determine who sees which portal.
- Distribution lists map to notification groups. When new training content is published to a category, the mapped AD group receives notifications.
- Nested groups are honored. If "Sales" is a parent group with "Sales - East", "Sales - West", and "Sales - Enterprise" nested underneath, each sub-group can have distinct content access while the parent group retains shared access to common sales resources.
The result: IT manages groups in one place (Active Directory), and every connected system, including the video platform, stays current.
Group-Based Access Rules Explained
Group-based access rules translate organizational structure into content permissions using a simple mapping logic.
- Department equals content category. The HR department group gets access to HR training videos. The Engineering group gets access to technical documentation recordings. The Finance group gets access to compliance training and earnings call recordings.
- Role equals permission level. Managers in a department get Contributor access (they can upload and organize). Individual contributors get Viewer access. Department heads get Manager access with analytics visibility.
- Location equals portal. Regional offices see their own localized content portal. A German office sees German-language training. A US headquarters sees the global library.
- Project equals collection. Cross-functional project teams mapped as AD groups get access to project-specific video collections for the duration of the project.
These rules run continuously. When group membership changes in Active Directory, the video platform adjusts access within the sync cycle. No tickets, no delays, no orphaned permissions.
Auto-Expiration and Time-Bound Access
Not every user needs permanent access. Contractors, seasonal workers, and project-based team members need access that ends when the engagement ends.
With identity-driven access control:
- Contractor accounts expire on end date. When the identity provider marks a contractor's account as expired, SCIM deprovisioning removes their video platform access the same day.
- Time-limited portal access. Training portals for a specific cohort (new hire class of Q1 2026, for example) can be tied to groups that are automatically dissolved after the training period.
- Project-based access. When a project team is disbanded and the AD group is deleted, video access for that project's recordings is revoked for all members.
- Guest access with expiration. External collaborators invited via limited-access URLs with time-based expiration do not need provisioning at all. The link expires, access ends.
This eliminates the "forgot to revoke" problem that plagues manual permission management.
How This Reduces IT Tickets and Security Risk Simultaneously
The operational impact of automating video access control is measurable in two areas.
Fewer IT tickets. Every "I can't access the training video" and "Please add this person to the video portal" ticket disappears when provisioning is automatic. For organizations with thousands of employees, this can mean hundreds of fewer tickets per quarter.
Reduced security surface. Orphaned accounts are the most common access control vulnerability in enterprise applications. Automated deprovisioning eliminates them. Permission drift is addressed by continuous sync rather than periodic audits. Audit trails show exactly when access was granted, modified, or revoked, and the identity provider event that triggered it.
For organizations in regulated industries (financial services, healthcare, government), automated access control also simplifies audit preparation. Instead of manually documenting who has access and when it was reviewed, the system maintains a continuous, auditable record. Healthcare organizations can read more about these requirements in the guide to HIPAA-compliant video training for clinical staff. Financial services teams will find similar considerations covered in the enterprise video platform guide for financial services.
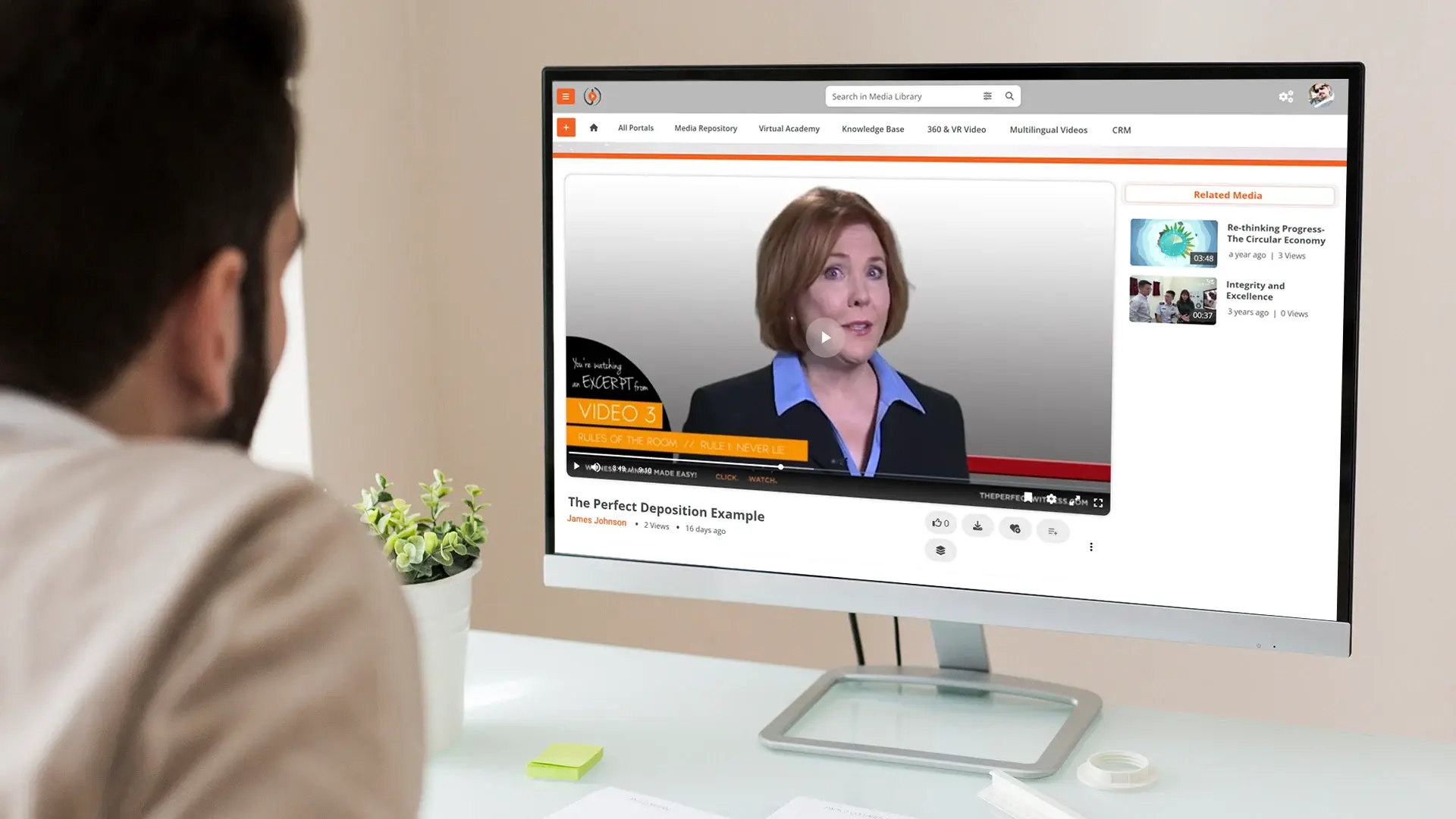
How VIDIZMO Enterprisetube Handles SCIM, SSO, and Group-Based RBAC Natively
VIDIZMO's platform supports automated access control as a core capability, not an add-on.
- SCIM provisioning. Native support with Azure AD, Okta, Ping Identity, OneLogin, and any SCIM-compliant identity provider. Accounts are auto-created, updated, and deactivated based on identity provider events.
- SSO integration. SAML 2.0, OAuth 2.0, and OpenID Connect. Works with Azure AD, Okta, Ping Identity, ForgeRock, OneLogin, ADFS, Google, and any compliant provider.
- MFA. Email OTP and additional authentication options for sensitive content portals.
- Role-based access control. Four-tier RBAC (Admin, Manager, Contributor, Viewer) at the portal, category, and content level, with permissions inherited down the hierarchy.
- Group-based content mapping. Identity provider groups map to content categories, portals, and permission levels. Membership changes propagate automatically.
- Portal security policies. Public, Private, and Custom access levels with IP whitelisting, domain restrictions, download restriction and geo-restrictions.
- Audit logging. Full access and modification trail with 3+ year log retention.
- Limited access URLs. Time-limited sharing links for external users who do not need full accounts.
Ready to automate video access control for your organization? Start your free EnterpriseTube trial to see SCIM provisioning and group-based RBAC in action.
People Also Ask
Yes. SCIM is a standard protocol. Any SCIM-compliant identity provider works, including Okta, Ping Identity, OneLogin, and ForgeRock. The video platform acts as a SCIM service provider, accepting provisioning events from any compliant source.
Yes. Each AD group can be mapped to a specific role (Admin, Manager, Contributor, or Viewer) and a specific content scope (portal, category, or collection). Nested groups can have distinct permissions from their parent group.
If the department change is reflected in Active Directory (moved from one group to another), the video platform access updates automatically on the next sync cycle. Old department content access is removed, and new department content access is granted.
With SCIM, deprovisioning is near real-time. When a user is disabled or deleted in the identity provider, the SCIM event triggers account deactivation on the video platform within the sync interval, typically minutes.
About the Author
Ali Rind
Ali Rind is a Product Marketing Executive at VIDIZMO, where he focuses on digital evidence management, AI redaction, and enterprise video technology. He closely follows how law enforcement agencies, public safety organizations, and government bodies manage and act on video evidence, translating those insights into clear, practical content. Ali writes across Digital Evidence Management System, Redactor, and Intelligence Hub products, covering everything from compliance challenges to real-world deployment across federal, state, and commercial markets.
Jump to
You May Also Like
These Related Stories

Enterprise Video Platform for Financial Services: Compliance & Security

How to Choose Video Library Management Software for Enterprises




No Comments Yet
Let us know what you think