Tamper Detection: How it Works to Keep Digital Evidence Safe?
by Moazzam Iqbal, Last updated: April 28, 2026 , ref:
.jpg)
According to statistics from the United States Courts, the median time from filing to disposition of a criminal case was approximately seven months in 2019, while civil cases averaged around ten months. In that year alone, more than 412,000 federal cases were filed.
These timelines reflect only the period to disposition. In practice, evidence must often be preserved well beyond that due to retention requirements and appeals. As a result, law enforcement agencies and regulated organizations manage large volumes of digital evidence over extended periods.
At this scale, maintaining evidentiary integrity becomes a critical operational concern. Evidence tampering, defined as the alteration or unauthorized manipulation of evidence, can directly impact admissibility and case outcomes.
Digital evidence introduces additional risk. Even minor, non-obvious changes to a file or its metadata may raise challenges in court. Detecting such changes manually across large repositories is neither efficient nor reliable.
For organizations responsible for safeguarding digital recordings and investigative media, tamper detection is a foundational control within a structured Digital Evidence Management System. Understanding how it works is essential to ensuring courtroom defensibility.
How Digital Evidence Tampering Occurs
Digital evidence can be compromised in ways that are not immediately visible. Unlike physical evidence, where alteration may leave observable signs, digital files can be modified without obvious indicators.
Tampering can occur intentionally or unintentionally during different stages of the evidence lifecycle.
1. Direct File Modification
A video file may be edited to remove, insert, or alter content. Even minor edits, such as trimming frames or adjusting timestamps, can impact evidentiary integrity. In some cases, compression or re-encoding may unintentionally modify file structure and metadata.
2. Metadata Manipulation
Metadata contains critical information such as creation date, device details, and file history. Altering metadata can misrepresent when or how evidence was captured. In legal proceedings, discrepancies in metadata may raise authenticity concerns.
3. Unauthorized Access or Copying
Without proper access controls, files may be viewed, copied, or exported by unauthorized users. Even if content is not visibly changed, undocumented access can weaken chain of custody.
4. Version Confusion During Redaction
Redaction is often necessary to remove sensitive information. If original and redacted versions are not clearly separated and documented, questions may arise regarding which file represents the authentic source.
5. Data Transfer Vulnerabilities
Evidence transferred between systems without secure logging or integrity validation may lose metadata or be exposed to modification during transit.
Why Manual Detection Is Not Sufficient
Manually detecting alterations in large digital evidence repositories is neither efficient nor reliable. Comparing file versions, tracking access events, or maintaining separate logs increases the risk of oversight and documentation gaps.
As evidence volumes grow and retention periods extend, manual controls become legally vulnerable. Automated tamper detection ensures integrity, traceability, and defensible evidence handling at scale.
How Tamper Detection Works
Tamper detection in a Digital Evidence Management System relies on layered technical controls that continuously verify file integrity and monitor activity throughout the evidence lifecycle.
1. Cryptographic Hash Generation at Ingestion
When a video file is uploaded into the system, a cryptographic hash value is generated. This hash acts as a digital fingerprint unique to that file. If the file is altered in any way, even slightly, the hash value changes. By recalculating and comparing the hash over time, the system can confirm whether the evidence remains intact.
2. Continuous Integrity Verification
Integrity checks are not limited to ingestion. The system can revalidate hash values whenever the file is accessed, exported, or prepared for court. This ensures that the evidence presented matches the original file captured.
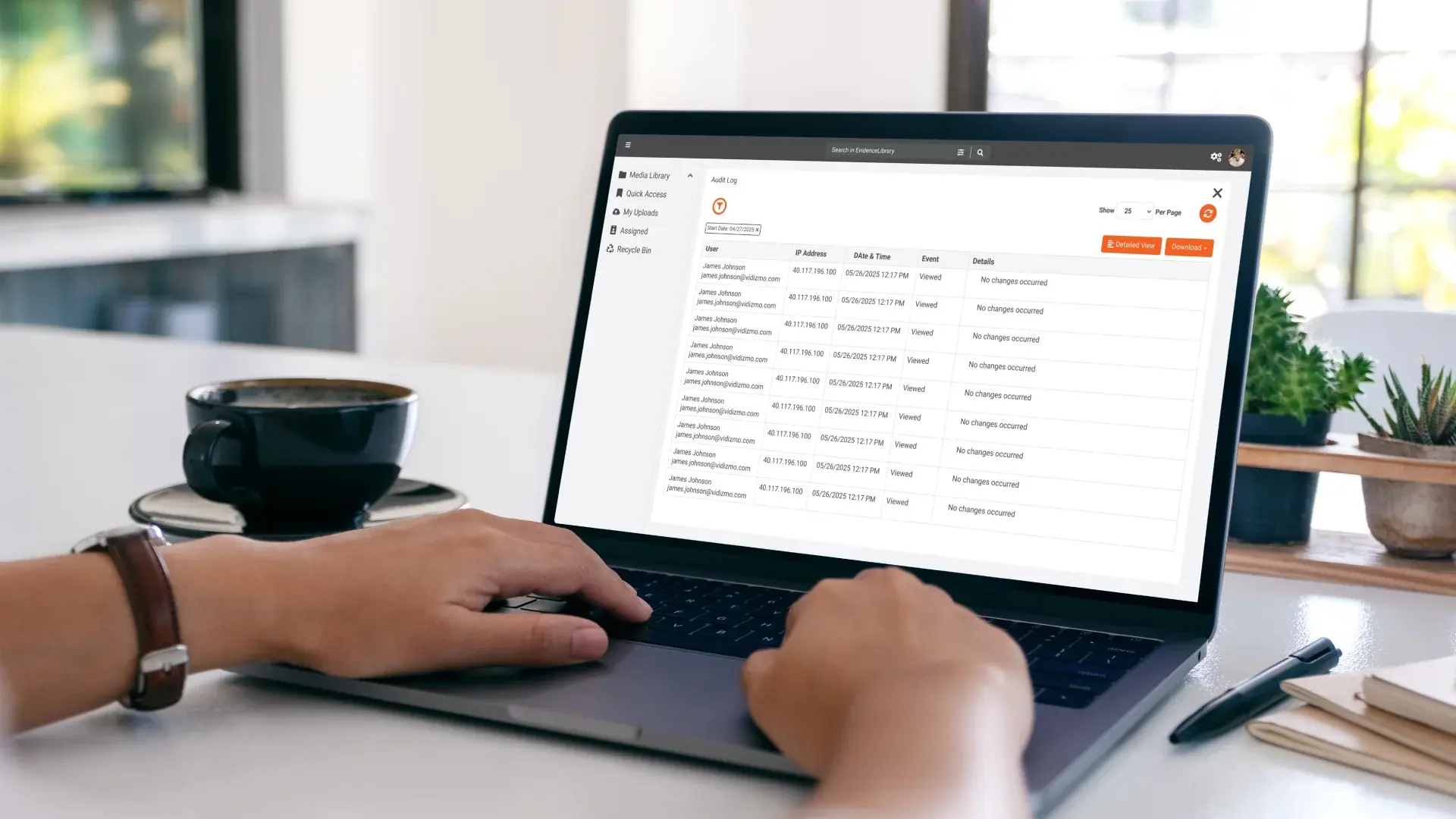
3. Immutable Audit Logging
Every interaction with the evidence is automatically logged, including access, transfers, redactions, and exports. These logs are system-generated and protected against modification, creating a defensible record of who interacted with the evidence and when.
4. Role-Based Access Controls
Granular permissions restrict who can view, manage, or export evidence. By limiting access and documenting activity, the system reduces the likelihood of unauthorized manipulation.
5. Version Control for Redacted Files
If redaction is required, the system preserves the original file while tracking any derived versions. This ensures that the source evidence remains unchanged and traceable.
Together, these mechanisms create a structured environment where any unauthorized modification can be detected and documented, strengthening courtroom defensibility.
Tamper Detection Across the Evidence Lifecycle
Effective tamper detection is embedded throughout the digital evidence lifecycle, including:
- Ingestion – Integrity validation occurs when the file enters the system.
- Storage – Files are protected against overwrite or deletion without authorization.
- Access – Every interaction is logged and traceable.
- Transfer – Secure sharing mechanisms preserve metadata and maintain auditability.
- Presentation – Integrity can be revalidated prior to courtroom submission.
By embedding tamper detection at each stage, organizations reduce procedural vulnerability.
Read more about how tamper detection secures digital evidence.
How Tamper Detection Supports Courtroom Defensibility
In legal proceedings, the ability to demonstrate that digital evidence has remained unchanged is critical. Cryptographic hash validation, immutable audit logs, and structured access controls provide verifiable documentation that can support testimony and withstand procedural scrutiny.
For agencies operating under CJIS or similar regulatory standards, enforced encryption, granular access governance, and activity traceability further reinforce evidentiary integrity.
When embedded within a Digital Evidence Management System, tamper detection transforms evidence handling from manual oversight into automated, defensible control, reducing procedural risk and strengthening courtroom credibility.
Implementing Tamper Detection in Practice
A purpose-built Digital Evidence Management platform embeds integrity validation, audit logging, and access governance directly into its core architecture, minimizing reliance on manual processes or disconnected tools.
VIDIZMO Digital Evidence Management applies layered tamper detection controls that preserve evidentiary integrity from ingestion through courtroom presentation, ensuring traceability at every stage.
To see how these controls function in practice, explore VIDIZMO Digital Evidence Management in more detail.
Key Takeaways
Tamper detection is a critical safeguard in digital evidence management. By combining cryptographic hash validation, immutable audit logs, role-based access controls, and version preservation, organizations can detect unauthorized changes and demonstrate evidentiary integrity. As digital evidence volumes grow and retention periods extend, automated tamper detection becomes essential for maintaining courtroom defensibility and reducing procedural risk.
People Also Ask
Tamper detection refers to the technical controls used to identify unauthorized alterations to digital files. In digital evidence management, it typically involves cryptographic hash validation, audit logging, and access governance to ensure that files remain unchanged from ingestion through presentation.
Digital evidence integrity is verified using cryptographic hash values. If a file is altered, even slightly, its hash value changes. Audit logs and access records also help determine whether unauthorized modifications or suspicious activity occurred.
In legal proceedings, evidence must be authenticated and proven unchanged. Tamper detection provides documented proof of file integrity and traceable access history, helping organizations defend against claims of alteration or mishandling.
Yes. Metadata such as timestamps, device information, or file history can be modified without visibly altering the content. This is why structured systems validate both file integrity and metadata consistency.
General cloud storage may provide security controls, but it typically lacks automated hash validation, immutable audit logs, and structured chain of custody tracking required for evidentiary defensibility.
About the Author
Moazzam Iqbal
Moazzam Iqbal is a Product Marketing Executive at VIDIZMO covering digital evidence management, enterprise video solutions, and AI-powered technology. He focuses on helping public safety agencies and government organizations make informed decisions about evidence and video infrastructure.
Jump to
You May Also Like
These Related Stories
Importance of Metadata and Audit Trails in Digital Evidence Management

Evidence Management Software for Law Enforcement: What It Does for Police




No Comments Yet
Let us know what you think