Prosecution Evidence Management: Why DA Offices Need a Modern Strategy
by Nadeem Khan, Last updated: May 15, 2026 , ref:
Prosecution evidence management is the discipline of receiving, preserving, organizing, and disclosing digital evidence across the life of a criminal case, from the moment a law enforcement agency hands off a file to the moment it appears on a courtroom monitor. For a district attorney's office, that workflow now spans body-worn camera footage, interview room recordings, surveillance video, mobile phone extractions, social media exports, and a growing pile of forensic reports. The volume isn't a back-office problem anymore. It's shaping conviction rates, Brady compliance, and how quickly cases clear the docket.
Most prosecutors didn't sign up to run a data operation. They signed up to try cases. But the gap between what law enforcement collects and what a courtroom can actually use has widened sharply since 2024, and the offices that close that gap are the ones winning trial preparation back from the disclosure deadline.
This guide walks through the strategic decisions that shape a modern prosecution evidence workflow, the regulatory pressure points DA offices need to know about in 2026, and the criteria that separate purpose-built platforms from repurposed law enforcement tools.
Key Takeaways
- Prosecution evidence management is structurally different from police evidence management. The receiving side, the disclosure side, and the retention rules are not the same.
- Brady and Giglio obligations are now enforced against digital evidence the same way they've always been enforced against paper. Missed video disclosure is the fastest-growing reversible-error category.
- The biggest cost in a DA office isn't storage. It's the attorney hours lost reviewing video that should have been auto-transcribed, tagged, and search-indexed on intake.
- Cloud is almost always the right call for offices under 500 staff. The capital cost of on-premises hardware rarely pays back at that scale.
- Evaluate platforms on three axes: ingest-side flexibility, disclosure-side control, and chain-of-custody defensibility. Anything that fails on one of those three will create a courtroom problem later.
Why is prosecution evidence management different from police evidence management?
Police evidence management is built around collection. Prosecution evidence management is built around receiving, disclosing, and preserving. The shape of the workflow flips at the handoff. A police Digital Evidence Management System (DEMS) optimizes for ingestion from cameras, devices, and field officers. A prosecution platform optimizes for case-bundle intake from multiple agencies, redacted disclosure to defense counsel, courtroom-ready presentation, and retention well past the conviction date.
From what we have seen across DA offices in 2025, the most common failure mode is treating the prosecution side as a downstream copy of the police system. It isn't. Felony cases routinely pull evidence from three or four agencies. Each agency uses a different platform, a different export format, and a different chain-of-custody record. The prosecutor inherits all of it and is legally responsible for whatever is missing.
The other structural difference is disclosure. A prosecution office produces evidence for defense counsel under specific rules (Federal Rules of Criminal Procedure, Rule 16, plus state analogs) on a clock. The platform has to support outbound sharing with full audit trails, time-limited access, and selective redaction. Most police-side products treat disclosure as a feature; for prosecutors, it's the core workflow.
What evidence does a prosecutor actually need to manage?
Short answer: anything that touches the case. The longer answer is that the inventory has shifted dramatically. A 2024 Bureau of Justice Assistance review of prosecutor caseloads found that digital evidence volumes per felony case had grown roughly 5x since 2018, driven mostly by body-worn cameras, mobile device extractions, and cloud-based service records.
A typical prosecution evidence inventory for a single case now includes:
- Body-worn camera footage from the responding officers, sometimes spanning multiple shifts
- Dash camera and in-car video from patrol and traffic units
- Interview room recordings, often multi-camera and synchronized to audio
- Surveillance and CCTV exports from private businesses, transit systems, and public infrastructure
- 911 audio and dispatch records
- Mobile device extractions from forensic tools like Cellebrite or GrayKey
- Social media and platform records returned under search warrants or subpoenas
- Forensic reports: DNA, ballistics, toxicology, digital forensics
- Photographs from scene processing
- Documents and transcripts generated during investigation
Every one of those formats has its own metadata, its own chain-of-custody record, and its own preservation requirement. A common mistake is to standardize everything on a single format at intake, which destroys evidentiary integrity. The platform needs to preserve originals, not normalize them away.
Why does Brady compliance hinge on your evidence platform?
Brady v. Maryland and the line of cases that followed (Giglio, Kyles, Smith) require the prosecution to disclose all material exculpatory and impeachment evidence to the defense. That obligation is independent of intent. A prosecutor who simply did not know a piece of evidence existed has still violated the rule.
Here's why this matters for evidence platforms. When video evidence sits in folders across multiple agencies, in different naming conventions, with no unified search, the probability that something exculpatory gets missed is meaningful. Since 2023, appellate courts have grown more willing to vacate convictions where the missed evidence was digital and where the office could not show a documented process for reviewing the full record.
The part most teams overlook is that Brady compliance is now a process question, not a memory question. Courts want to see that the office can produce, on demand, a full inventory of what evidence existed, who had access to it, when it was reviewed, and what was disclosed. If your platform cannot answer those four questions in a single audit log, you have a vulnerability.
A 2025 Police Executive Research Forum survey of prosecutors found that 58% of respondents had experienced at least one case where digital evidence disclosure was challenged on Brady grounds. The platform-level controls that prevent those challenges are auditable access logs, end-to-end chain-of-custody records (NIST SP 800-86 provides the federal framework), and exportable disclosure receipts.
How should DA offices think about cloud versus on-premises?
This is the question that paralyzes more procurement committees than anything else, and we have an opinion on it. For offices under 500 staff, cloud is almost always the right call. The capital expense, refresh cycle, and security personnel required for on-premises hardware rarely pay back at that scale. The math changes for large state offices and federal districts, where data sovereignty rules, classified workloads, or air-gapped requirements force on-premises or government-cloud deployments.
The decision should be driven by three factors:
- Compliance posture. If the office handles federal cases or works closely with federal partners, FedRAMP High or IL4/IL5 environments are non-negotiable. Those deployments live in government clouds (Azure Government, AWS GovCloud) rather than commercial regions.
- Data sovereignty. State open-records laws and discovery rules sometimes restrict where evidence can be stored. A handful of states require in-state hosting for certain case types.
- Total cost of ownership. On-premises looks cheaper on paper until you count storage refresh, security staff, backup infrastructure, and the audit cost of proving compliance every year.
One thing worth flagging: hybrid deployments have become more common since 2025. Many offices keep an on-premises tier for ultra-sensitive cases (homicide, public corruption, ongoing investigations) and use cloud for everything else. The platform needs to support that split without forcing two separate systems.
What does a defensible chain of custody look like for digital evidence?
Chain of custody for digital evidence is fundamentally about answering one question: can you prove this file is unchanged from the moment it was collected? The answer rests on cryptographic hashing, immutable audit logs, and access controls.
The federal framework is NIST SP 800-86, Guide to Integrating Forensic Techniques into Incident Response. State courts have generally followed the same principles, with some variation on what counts as a sufficient hash algorithm. SHA-256 is the current floor. SHA-1 is no longer acceptable for new evidence in most jurisdictions.
A defensible chain of custody requires:
- Hash-on-ingest. Every file gets a cryptographic hash the moment it lands in the system. The hash is recorded, not just the file.
- Hash verification on every read. Any time the file is accessed, viewed, or exported, the hash is recomputed and compared. Mismatches trigger alerts.
- Tamper-evident audit logs. Every access event (user, IP, timestamp, action) is recorded in a log that cannot be silently edited.
- Role-based access control (RBAC). Not everyone in the office should be able to open everything. Access is granted by role and case assignment.
- Exportable chain-of-custody reports. When the case goes to trial, the office needs to produce a printable record of every event in the file's history.
From what we've seen, the gap most platforms have is in the second item: hash verification on every read. Many systems hash at ingest and never check again. That isn't enough to satisfy a motion to suppress on integrity grounds.
How does AI change the prosecution evidence workflow?
AI is now the difference between a case taking 80 attorney hours of review and 20. The technology that matters most for prosecution work is transcription, redaction, object and event detection, and summarization. These aren't gimmicks. They directly compress the review cycle.
Auto-transcription with searchable transcripts means an attorney can find every mention of a name, location, or phrase across a 14-hour interrogation file in seconds. Auto-redaction for victim faces, witness identifiers, and bystander PII compresses what used to be days of frame-by-frame editing into a review pass on flagged regions. Object detection surfaces weapons, vehicles, license plates, and faces of interest without manual scrubbing.
One thing worth flagging: AI accuracy is a function of language, audio quality, and speaker count. A clean two-speaker interview transcribes near-perfectly in English. A four-speaker domestic-violence call with overlapping speech and background noise will need human verification. The right operational model is AI-first, human-verified for anything that will hit a courtroom. Treat AI as a force multiplier on attorney review, not a replacement for it.
Why disclosure to defense counsel is the test of any platform
If you want to evaluate a prosecution evidence platform in 30 seconds, ask how it handles disclosure to defense. The answer reveals whether the product was built for prosecutors or repurposed from a police system.
Good disclosure requires time-limited access links, watermarked exports, read-only viewing, full audit trails of what defense counsel viewed and when, the ability to share redacted versions while preserving unredacted originals, and selective sharing at the file or case-folder level. It also requires a path for defense counsel to view evidence without downloading it, which is increasingly the standard in jurisdictions concerned about evidence leaking to media or social platforms.
The historical pattern of burning evidence to a DVD or USB drive and handing it across the table is breaking down. Federal Rule 16 disclosure timelines and state analogs increasingly assume electronic delivery, and defense bar associations have begun pushing back on offices that still insist on physical media.
What standards and compliance frameworks apply?
Prosecution offices operate under a stack of overlapping standards. The platform has to support all of them, not just the ones the IT team thinks about first.
| Framework | What It Covers | Why It Applies to Prosecutors |
|---|---|---|
| FBI CJIS Security Policy v5.9.5 | Encryption, access control, audit, and personnel requirements for criminal justice data | Mandatory for any office accessing CJI from law enforcement systems |
| FRCP Rule 16 / Brady doctrine | Discovery and exculpatory evidence disclosure | Defines the disclosure obligation the platform must support |
| NIST SP 800-86 | Digital forensic chain-of-custody framework | Reference standard for evidence integrity in federal cases |
| FedRAMP High / NIST SP 800-53 Rev. 5 | Cloud security baseline for federal data | Required for offices handling federal cases or partnering with federal agencies |
| NARA General Records Schedule | Federal records retention rules | Provides the retention framework many state schedules are modeled on |
| State open records laws | Public access to government records | Defines what evidence must be disclosed under public records requests, and what is exempt |
The compliance language matters here. A platform "supports CJIS-compliant deployments" when run on Azure Government. It isn't itself CJIS-certified, because CJIS is an operational policy, not a product certification. Be careful with vendor claims that conflate the two. That distinction will come up in any serious procurement review.
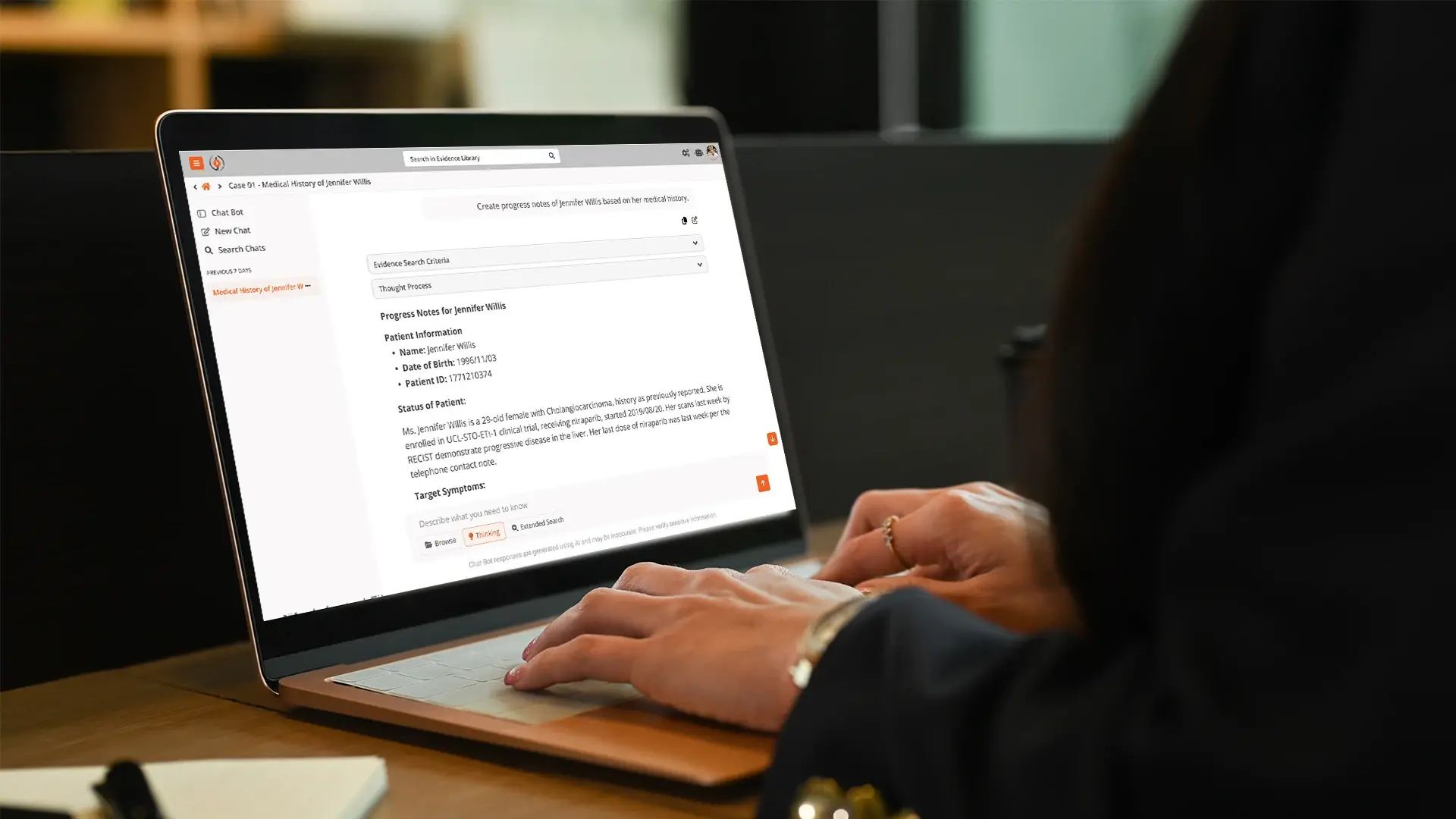
How VIDIZMO fits into a prosecution evidence strategy
VIDIZMO DEMS provides three capabilities that map directly to the prosecution workflow described above. First, multi-agency intake: the portal-based architecture lets each contributing agency upload into a segregated workspace within a single case, preserving their chain of custody while giving the prosecution a unified view. Second, AI-assisted review: transcription across 82 languages with published WER benchmarks, auto-redaction, object detection, and a RAG-powered investigation assistant that lets attorneys query the full case file in natural language. Third, defensible disclosure: time-limited links, watermarked exports, full audit trails, and exportable chain-of-custody reports built on SHA-256 hash verification.
VIDIZMO DEMS supports CJIS-compliant deployments on Azure Government, FedRAMP High and IL4/IL5 deployments via Azure Government Cloud where required, and on-premises or air-gapped configurations for sensitive cases. For DA offices that need to coordinate across federal, state, and local partners on the same case, the deployment flexibility removes the cross-system handoff problem that creates most Brady-compliance gaps.
Frequently Asked Questions
What does evidence management mean in a prosecution context?
Evidence management in a prosecution context means the disciplined process of receiving digital evidence from multiple law enforcement agencies, preserving its integrity through cryptographic hashing and audit logs, organizing it by case, supporting attorney review, and disclosing it to defense counsel under court rules. It's distinct from police evidence management, which is collection-oriented.
What are the 4 P's of evidence?
The 4 P's are Preserve, Protect, Process, and Present. Preserve covers initial collection and hash-based integrity. Protect covers access control and chain of custody. Process covers analysis, transcription, redaction, and tagging. Present covers courtroom-ready playback and disclosure. A modern prosecution evidence platform should support all four phases in one system rather than forcing handoffs between tools.
What are the 7 types of evidence?
Legal practice typically recognizes seven categories: real (physical objects), demonstrative (charts, models, recreations), documentary (records, contracts, transcripts), testimonial (witness statements), digital (electronic files, video, audio), forensic (DNA, ballistics, toxicology), and circumstantial (inferential). Digital and forensic evidence are the fastest-growing categories and the ones most affected by platform choices.
What evidence does a prosecutor need?
A prosecutor needs everything material to the case, both inculpatory and exculpatory, in a format that is preserved, searchable, and disclosable. The legal floor is set by Brady, Giglio, and state discovery rules: anything that could be material to guilt, punishment, or witness credibility must be available for review and disclosure. Practically, that means video, audio, documents, forensic reports, and metadata from every contributing agency.
How does cloud-based evidence management compare to on-premises for DA offices?
For offices under roughly 500 staff, cloud-based platforms typically cost less over a five-year window and offer better security than self-managed hardware. On-premises makes sense for large state offices, federal districts, and any case workload involving classified or air-gapped requirements. Hybrid deployments, where sensitive cases live on-premises and the bulk of the workload runs in cloud, have become common since 2025.
What is the role of AI in prosecution evidence review?
AI compresses attorney review time on transcription, redaction, search, and summarization. A 14-hour interrogation file that used to take 20 hours to review can be searchable and tagged within an hour of ingest, with the attorney verifying AI output rather than starting from scratch. The right operational model is AI-first, human-verified for anything that will be presented in court.
How do you maintain chain of custody for digital evidence?
Maintaining chain of custody for digital evidence requires SHA-256 hashing at ingest, hash verification on every read, tamper-evident audit logs of every access event, role-based access controls, and exportable chain-of-custody reports. The federal framework is NIST SP 800-86. State courts generally follow the same principles, though specific hash algorithm requirements vary.
Where to go from here
Prosecution evidence management isn't a back-office function anymore. It's a strategic capability that affects conviction rates, Brady compliance, and the office's ability to clear cases inside statutory deadlines. The offices that treat it as a platform decision, rather than a storage decision, will be the ones reading fewer reversal opinions and winning more pre-trial motions in 2026 and beyond.
If your office is rethinking the evidence stack, or trying to coordinate intake from multiple agencies on the same case, schedule a platform consultation to walk through how the workflow would look in your jurisdiction. For a feature-level walkthrough of the underlying DEMS capabilities (multi-agency portals, AI investigation assistant, disclosure controls), the deep technical detail lives at digitalevidence.ai.
External references used in this guide: Federal Rules of Criminal Procedure, Rule 16, Bureau of Justice Assistance, NARA General Records Schedule, and NIST Privacy and Forensic Framework references.
About the Author
Nadeem Khan
Nadeem Khan is the CEO and co-founder of VIDIZMO, where he has led the company's growth from a video management startup into an AI-powered platform trusted by federal law enforcement, defense agencies, and Fortune 500 enterprises. He spearheaded the development of VIDIZMO's Digital Evidence Management System, now used by leading public safety agencies across North America. With over 25 years in enterprise software architecture and cloud infrastructure, Nadeem brings hands-on technical depth to every product decision. Before taking the CEO role, he served as CTO and Chief Architect at VIDIZMO and spent 17 years as Principal Consultant at Softech Worldwide, a Microsoft Gold Partner. He holds a BS in Electronics from NED University of Engineering and Technology.
Jump to
You May Also Like
These Related Stories

Automated Police Report Generation from Multi-Source Evidence in 2026

AI Case Timeline Generation: Build Prosecutor Chronologies Faster



No Comments Yet
Let us know what you think